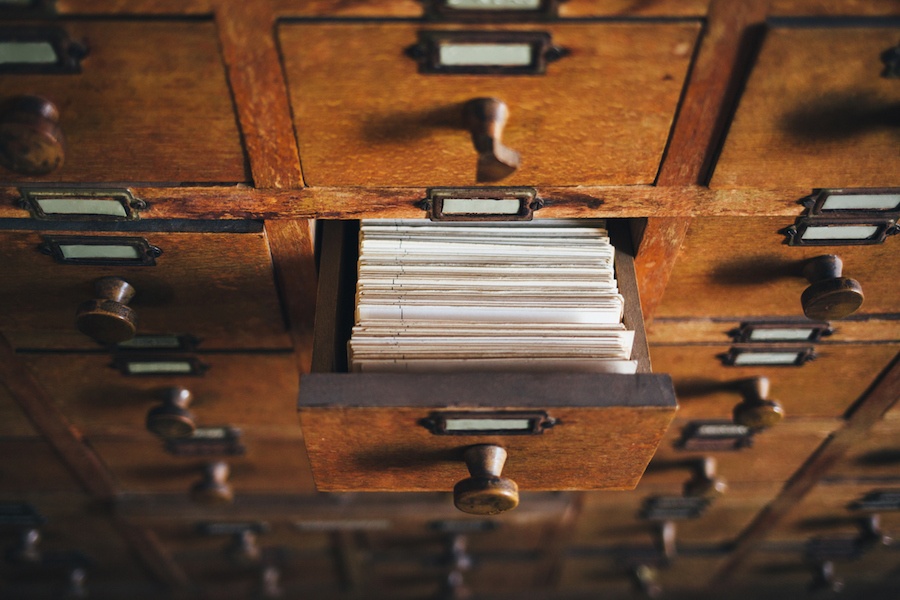
The Cabinet Files incident is all over the news - and not only is the public shocked by the content of the sensitive documents, but also by the way the data was lost through poor record management practices.
A filing cabinet containing sensitive documents was allegedly found at a second-hand furniture store, inside a second-hand filing unit. The owner of the filing cabinet then leaked the information to the press.
For Kyocera, The Cabinet Files incident provides a perfect example of the risks of poor record management.
Of course, hindsight is 20/20, but Branko Kondic, Kyocera's General Manager of NSW, and Milan Vukovic, KYOCERA’s Solutions Product Manager, have some top tips on how to prevent sensitive information flowing out of your business’ front door.
These documents seem to have been treated with a casual attitude towards storage and security.
B: What surprised me is that this has all happened since the advent of digital document management - with so much technology to manage physical records and information, where are the protocols, rules, procedures, and auditing trails.
These are documents that date back several years, and for organisations - and especially the government - to continue to have poor record management procedures in place for sensitive material is just negligent.
M: Yes, we work with a lot of government bodies, and each time we do, we have to go through a lot of hurdles because they require a high level of security - so to see this happen is quite unsettling.
Clearly, nobody knew these documents were inside the filing cabinet.
M: Well, it’s much harder to find information when it’s stored on paper in some filing cabinet. Users can only search by one or two filters, depending on how physical files are stored. Some organisations need to have a filing cabinet of the master records (what will happen if someone loses a filing cabinet with the master record list?). With information access system, you can easily apply as many search criterias as you like or perform full text search.
B: I think it’s easy to blame the individual who misplaced the filing cabinet, but who’s taking ownership of the process - who’s managing it? Organisations should be scanning and securely shredding the documents. That’s where the big issue is. So it’s ultimately up to the head of the department.
To be more effective, companies need to digitise. You should be scanning and storing documents instead of having them lying around - they become a liability. If the information wasn’t on a piece of paper in the filing cabinet, and instead it was stored digitally, the chances of it being misplaced would be a lot lower.
M: Of course, even though there are protocols and securities around digital file storage, people can make mistakes. For example, people can lose their laptops or leave USBs lying around - and information has certainly been leaked that way - there’s just more risk with paper, since it’s the most exposed medium e.g. someone can take snapshot or copy of documents.
This is the reason why sensitive documents should not be stored on laptops, USB’s or paper. Storing sensitive documents to an information access system provides secure access to documents at demand without security risks.
Additionally there is risk of paper documents to be destroyed in natural disasters. Say there’s been a fire, then you’ve lost the record completely, whereas if it has been digitised and stored in information access system, there will be a backup copy of that file.
A question on everyone’s minds is: who else has seen these documents? There is no way of knowing who has seen them, copied them, passed them onto others - while with information access system there is audit trail.
B: Exactly - with physical documents there’s no record of access. Someone can look at it, copy it and you won’t know.
That’s why these documents should have been digitised on receipt within the department, and then there should have been an electronic workflow process with records in terms of who can see the information. As soon as the documents are digitised or put through a secure workflow information access system, you can secure them by making sure the right people view the right documents at the right time.
After they were digitised they should have then been securely disposed of - by incineration or shredding, and you can get a certificate of destruction if required.
M: Due to the nature of some documents, there are solutions that permanently redact sensitive information like credit card numbers. Or operators can only see different part of information and never whole documents.
The documents themselves reveal other security breaches. Just how dangerous is information in the hands of external parties?
B: All information has the potential to be used against its originator. The risk depends on the kind of data that’s been breached:
- From a B2B perspective, it could expose an organisation’s weak points.
- From a government perspective, it’s a matter of national security.
- From the point of view of an individual whose private records (eg. related to health or finances) have been leaked, it’s a matter of identity or personal security.
The biggest benefit of digitising your documents is having secure, auditable access to documents - and you ensure that you’re showing the right document to the right person at the right time.
You do this by placing limits on what is and is not seen by the user. A partial credit card number is a good example of this - and limits the requirement to see this information to those who actually need it.
What are the 3 biggest lessons governments and departments can learn from this incident?
To prevent poor record management and ensure incidents like this don't occur, organisations need to:
1. Work with specialist suppliers to develop solutions that provide a high level of security, accessibility, and auditability of sensitive information.
The aim is to have stringent processes around transferring, encrypting, storing and archiving documents. Documents should be securely stored with certificates.
There are plenty of solutions in the marketplace - and while some can be pricey, we’ve seen through this incident just how much is at stake.
2. Don’t be complacent about taking steps to digitise information. It starts from above. This is the way that modern organisations are managing their data, and it’s for a good reason - there is much to gain and little to lose.
3. Implement the processes and procedures for an information management system - and be sure to implement at all levels of your organisation, because if people aren’t trained or don’t know about it then these kinds of leaks are bound to occur.
The interplay of print and document security is increasingly complex in the era of remote work. But Kyocera customers can count on our industry-leading expertise and proven ability to protect their business. Download our guide to learn more about our specialised document security solutions.