Business phishing scams are one of the top cybersecurity threats in Australia.
According to the Norton SMB Cyber Security Survey, 54% of Australian businesses that experienced a cyber attack in 2017 fell victim to an email or business phishing scam. These data breaches can also be costly, particularly to SMBs, with the same survey reporting that cyber attacks cost businesses an average of $10,299 each.
Recent data breaches have made business even more vulnerable to phishing, with Facebook reporting a data breach affecting 29 million accounts, exposing data such as birth dates, employers and education history, all of which can potentially be used by attackers to make phishing emails more credible.
To help Australian businesses combat this threat, and protect themselves from costly data breaches, here is a quick-fire guide to business phishing scams, how they work, and how to defend against them. This is an excerpt from our ebook, The Ultimate Guide to Securing Your Business Data.
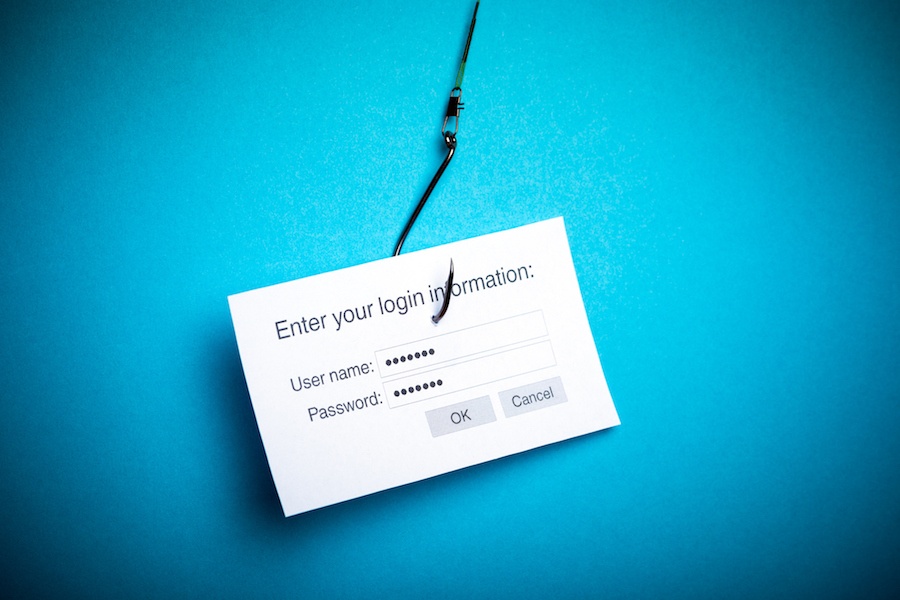
What are business phishing scams?
Phishing scams are a type of cyber attack that uses deceptive emails, phone calls, text messages and websites.
The goal is to trick recipients into proving personally identifiable information (PII) like contact details, bank account and credit card numbers, and even usernames and passwords.
Phishing scams could also entice people to click a link to a fake website or download an attachment with malicious software or malware.
How phishing works
A business phishing scam attack usually includes these steps:
- A fraudulent email is sent to a large number of unsuspecting recipients.
- The email uses the same branding and logo as popular brands. Phishing emails often pretend to be from banks, credit card businesses, telephone companies, courier services, social media sites and payment providers.
- The emails ask recipients to verify personal details, confirm a package delivery, claim a prize or complete a survey. They may even pretend to be from a software company, internet service provider or security firm informing you of some ‘suspicious activity’ on your account.
- The objective of a phishing email is to encourage people to click on a link to a fake website, reply to the email or call a number – and provide sensitive information. These personal details can then be sold to criminals or used to steal your money and identity.
- Phishing emails frequently tempt victims to open an attachment. The downloaded file can contain a virus, ransomware or any type of malware that will compromise the system, server or network.
However, as people are becoming more aware of the dangers of opening unsolicited attachments, some scammers now invite targets to google the name of a company and use SEO tactics to drive people to a corrupted website.
3 ways to protect your business from phishing scams
With business phishing scams on the rise in Australia, it is important that you take the necessary measures to protect your staff members and business.
To do that you can:
1. Install the necessary protection software
Start by installing the latest firewall, spam filter, anti-virus and anti-spyware software on all your computers, devices and servers.
This process is often overlooked and forgotten. But it’s important to keep your protection technologies up-to-date, so spam and phishing emails can be filtered out before they reach your employees.
2. Monitor website, email and network activities
Protect your systems and data through complete control and visibility across your networks. This includes setting up automated solutions to track website traffic, email communications and activities.
Setting up automated monitoring solutions alerts you to any hacking attempt or malware infiltration.
3. Educate your staff
This is perhaps the most important step in protecting your business from phishing attacks.
- Train and educate all your employees on the dangers of opening suspicious emails or clicking unverified website links.
- Remind them to never give out personal or sensitive information via email, and without confirming the validity of the source.
- Create clear policies and procedures on how to respond and report a suspected phishing attack or any other cyber security issue.
In the end, your employees have the potential to be the weakest link in your cybersecurity defence – and this is exactly what cyber attackers bank on. That’s why you need a multi-layered approach.
By using technology to filter out phishing emails and detect system abnormalities, and by ensuring employees are regularly educated about phishing scams and how to detect them, you can significantly reduce the risk of a data breach.
Every organisation is a potential target for cybercriminals. Business leaders must be alert to the current threats in order to protect their company from attack. Download our guide to learn everything you need to know about business cybersecurity and securing your business data.